Microsoft’s controversial AI-powered Recall feature, designed to offer a "photographic memory" of a user’s PC activity, faces renewed scrutiny following the public disclosure of a significant security flaw by researcher Alex Hagenah. Hagenah’s findings, detailed on the TotalRecall GitHub page and through his TotalRecall Reloaded tool, highlight a critical vulnerability not in the secure storage of Recall data, but in its processing and transmission after user authentication, allowing for the unauthorized exfiltration of sensitive information without requiring administrator privileges. Despite the detailed demonstration of this exploit, Microsoft has officially classified the issue as "not a vulnerability" and has indicated no plans for a fix, a stance that has ignited further debate within the cybersecurity community regarding user privacy and the responsible deployment of AI technologies.
The Genesis of Controversy: Understanding Microsoft Recall
To fully grasp the implications of Hagenah’s discovery, it is essential to understand the context surrounding Microsoft Recall. Announced as a flagship feature for Microsoft’s new Copilot+ PCs, Recall is designed to continuously capture screenshots of a user’s desktop activity, creating a searchable timeline of everything they have seen or done on their computer. This "photographic memory" aims to enhance productivity by allowing users to quickly revisit past interactions, documents, or web pages using natural language queries powered by AI.
From its initial announcement, Recall was met with immediate and widespread privacy concerns. Cybersecurity experts, privacy advocates, and even mainstream media outlets raised alarms about the feature’s potential for mass surveillance. Critics highlighted the sheer volume of sensitive personal and professional data that Recall would accumulate, ranging from private conversations and financial details to confidential documents and medical information. The prospect of such an extensive digital archive, even if stored locally, sparked fears of potential misuse, unauthorized access, and the creation of a massive honeypot for cybercriminals.
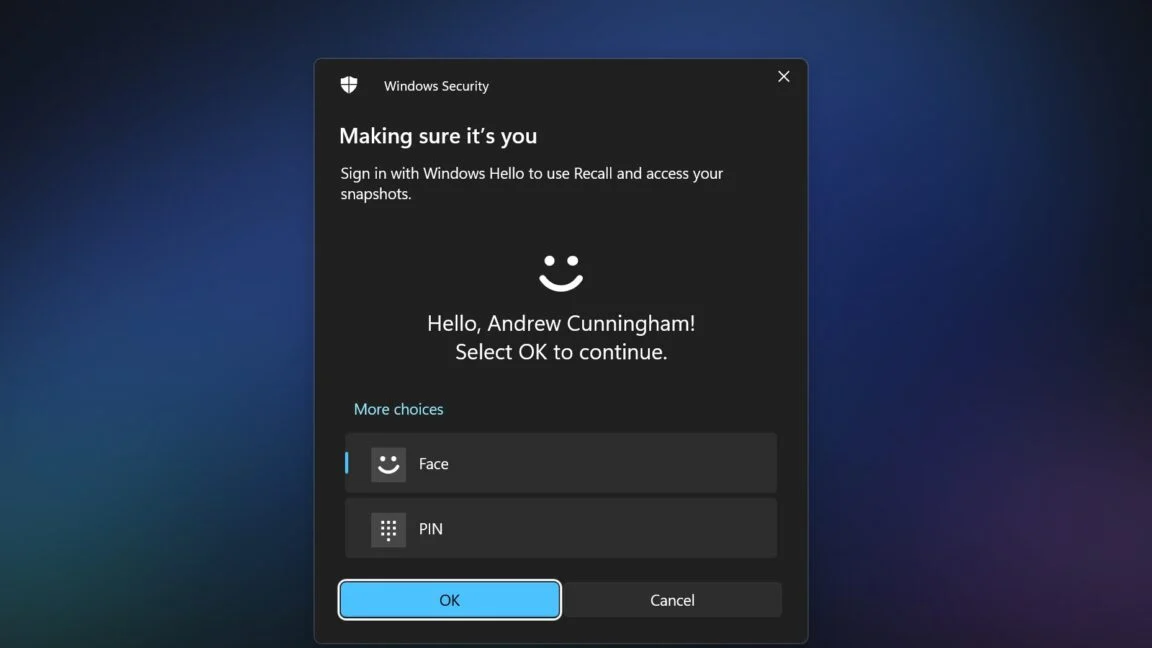
Microsoft initially attempted to assuage these concerns by emphasizing that Recall data would be stored locally on the user’s device, encrypted, and processed within a secure Virtualization-Based Security (VBS) enclave. They also stated that the feature would be opt-in and would require Windows Hello authentication for access. These measures were intended to assure users that their data would remain private and secure. However, the underlying concept of continuously logging user activity, regardless of the security measures, remained a significant point of contention. The "Always-on" nature of Recall, even when minimized, meant that a comprehensive record of a user’s digital life was constantly being built, raising the attack surface for potential adversaries.
The Chink in the Armor: The AIXHost.exe Vulnerability
Alex Hagenah’s investigation into Recall’s architecture uncovered a critical weakness that challenges Microsoft’s assurances of "rock solid" security. According to Hagenah, the core database where Recall stores its captured data is indeed well-protected, residing within a VBS enclave and requiring Windows Hello authentication for decryption. This "vault," as he metaphorically describes it, is robust.
However, the problem arises in the subsequent step of data processing. Once a user successfully authenticates using Windows Hello and accesses Recall, the system passes this sensitive data – including screenshots, OCR’d text, and various metadata – to another system process known as AIXHost.exe. It is this "delivery truck" that, in Hagenah’s assessment, lacks the same stringent security protections as the initial data vault. Unlike the Recall database itself, AIXHost.exe does not benefit from the enhanced security features of the VBS enclave, leaving it vulnerable to specific types of attacks.
Hagenah’s analogy powerfully illustrates the flaw: "The vault is solid," he writes, "The delivery truck is not." This means that while the data might be securely stored at rest, the moment it is moved for processing or display, it enters a less protected environment, creating an opportunity for interception.
TotalRecall Reloaded: Demonstrating the Exploit
To demonstrate the practical implications of this vulnerability, Hagenah developed a tool called TotalRecall Reloaded. This tool leverages a sophisticated technique to exploit the weakness in AIXHost.exe. The core mechanism involves using an executable file to inject a Dynamic Link Library (DLL) file into the AIXHost.exe process. Crucially, this DLL injection can be performed without requiring administrator privileges, a fact that significantly lowers the barrier for attackers and makes the exploit far more dangerous. Many sophisticated malware strains operate without elevated privileges to avoid detection and maintain persistence.
Once the malicious DLL is injected, TotalRecall Reloaded lies dormant in the background, patiently waiting for a specific trigger: the user opening Recall and authenticating with Windows Hello. Hagenah explicitly states that his tool does not bypass Windows Hello authentication itself. Instead, it "makes the user do it, silently rides along when the user does it, or waits for the user to do it." This distinction is vital; the exploit capitalizes on the legitimate user interaction, turning a secure authentication step into an enabler for data theft.
Upon successful user authentication, the injected DLL within AIXHost.exe can intercept the flow of data. This includes newly captured screenshots, the Optical Character Recognition (OCR) text extracted from those screenshots, and other critical metadata that Recall sends to the AIXHost.exe process for display and further processing. A particularly concerning aspect of this exploit is its persistence: the tool can continue to intercept data even after the user closes their Recall session, meaning ongoing surveillance can occur without the user’s immediate awareness or continued interaction with the Recall interface.
The scope of data accessible through this method is comprehensive. Hagenah states that once authenticated, TotalRecall Reloaded can access both new information being recorded to the Recall database as well as historical data that Recall has previously captured. This means an attacker could gain a complete picture of a user’s past and present digital activities.
Furthermore, Hagenah identified a set of tasks that do not even require Windows Hello authentication to perform. These include:
- Grabbing the most recent Recall screenshot.
- Capturing select metadata about the Recall database.
- Deleting the user’s entire Recall database.
This baseline level of access, even without full authentication, already presents a significant risk, allowing an attacker to quickly ascertain information about a user’s current activity or even destroy evidence. The ability to delete the entire database could be used by an attacker to cover their tracks or to disrupt the user’s system.
A Timeline of Disclosure and Disagreement
The chronology of Hagenah’s discovery and Microsoft’s response is critical to understanding the current impasse.
- March 6, 2024: Alex Hagenah, after identifying the flaw, responsibly reported his findings to Microsoft’s Security Response Center (MSRC), adhering to standard vulnerability disclosure practices. This proactive reporting provided Microsoft with ample time to assess the issue before the public release of Recall.
- April 3, 2024: Following its internal assessment, Microsoft officially classified Hagenah’s findings as "not a vulnerability." This decision signaled that Microsoft did not intend to address the reported issue through a security patch or modification.
- May 20, 2024: Microsoft officially announced the Copilot+ PCs, prominently featuring the Recall capability, despite the outstanding security concerns that had been internally dismissed. This timing is significant, as it indicates Microsoft moved forward with the feature’s launch knowing about the reported flaw and its classification.
- Early June 2024 (approx.): Hagenah publicly disclosed his findings, including the TotalRecall Reloaded tool, following Microsoft’s decision not to classify it as a vulnerability and proceeding with the feature’s rollout. This public disclosure aimed to inform users and the broader security community about the inherent risks.
Microsoft’s stance that this is "not a bug" or "not a vulnerability" likely stems from a narrow definition of what constitutes a security flaw. From their perspective, if an attacker needs to have local access to a machine and the user needs to perform an action (like authenticating with Windows Hello), then the system’s core security mechanisms (like the VBS enclave for the database) are not being directly bypassed. They might argue that the risk is mitigated by the need for prior local compromise or user interaction, placing the responsibility on general system hygiene and user vigilance rather than a flaw in Recall itself. However, this interpretation clashes sharply with how many cybersecurity professionals view practical attack vectors.
Reactions from the Cybersecurity Community: A Deepening Divide
Microsoft’s dismissal of Hagenah’s findings as "not a vulnerability" has been met with significant skepticism and criticism from the cybersecurity community. Experts argue that classifying an exploit that allows local privilege escalation (from standard user to data exfiltration) without admin rights, and persistence, as "not a vulnerability" is problematic.
Many security researchers believe that any mechanism allowing sensitive data to be exfiltrated from a system without the user’s explicit consent, especially when it leverages an internal process that lacks the same robust security as the data’s primary storage, constitutes a serious security flaw. The fact that the exploit operates without administrator privileges is particularly concerning, as it means a relatively unsophisticated piece of malware, or even a malicious insider with standard user access, could compromise user data.
Troy Hunt, a prominent security researcher, has been vocal about the broader privacy implications of Recall, even before Hagenah’s discovery. The general sentiment among experts is that Recall, by its very nature, creates an irresistible target for attackers. Hagenah’s work only validates these initial fears, demonstrating a concrete method for exploiting the feature.
This ongoing disagreement highlights a fundamental difference in perspective: Microsoft appears to be focusing on the integrity of the secure enclave where data is stored, while the cybersecurity community is looking at the entire attack surface, including the processes that handle data after it leaves that secure enclave. The consensus among many professionals is that security must be end-to-end; a "solid vault" is meaningless if the "delivery truck" carrying its contents is easily compromised. The "not a vulnerability" classification risks setting a dangerous precedent, potentially minimizing other similar post-authentication attack vectors in the future.
Broader Implications and Risks
The implications of Hagenah’s findings, coupled with Microsoft’s response, extend far beyond a single technical flaw.
-
Exacerbated User Privacy Concerns: For individual users, this vulnerability means that even if they opt-in to Recall and use Windows Hello, their highly personal data – screenshots of banking information, private messages, medical records, or confidential documents – could be silently intercepted by malware that has gained local access. The promise of privacy through local storage and encryption is undermined by the vulnerability in the processing pipeline.
-
Significant Enterprise Risk: For businesses, the implications are particularly severe. Deploying Copilot+ PCs with Recall enabled could expose corporate secrets, intellectual property, and sensitive customer data. An attacker who gains even limited access to an employee’s machine could potentially exfiltrate vast amounts of competitive intelligence or personal identifiable information (PII), leading to massive financial losses, reputational damage, and severe regulatory penalties under laws like GDPR, HIPAA, or CCPA. Compliance officers and IT security teams will likely advise against enabling Recall in corporate environments unless Microsoft implements a robust fix.
-
Increased Attack Surface for Malware and Social Engineering: The fact that the exploit relies on user authentication makes it a prime candidate for social engineering tactics. Phishing campaigns could trick users into running malicious software that then lies in wait for them to legitimately access Recall. This type of "ride-along" attack is notoriously difficult for users to detect, as their interaction with the legitimate Recall feature appears normal. The low-privilege requirement also makes it an attractive target for advanced persistent threats (APTs) seeking to maintain a stealthy presence on compromised systems.
-
Erosion of Trust in Microsoft: This incident, building on the initial public outcry surrounding Recall, further damages Microsoft’s reputation as a steward of user privacy and security, especially in the rapidly evolving landscape of AI. The company’s decision to dismiss a demonstrable exploit as "not a vulnerability" can be perceived as dismissive of legitimate security concerns and indicative of prioritizing feature rollout over user protection. This could have long-term consequences for user adoption of future AI-powered features and Microsoft products in general.
-
Ethical Considerations in AI Development: The Recall controversy and its associated security flaws bring to the forefront the ethical responsibilities of technology companies in developing powerful AI features. When features collect such extensive user data, the onus is on the developer to ensure not just the theoretical security of the storage, but the practical, end-to-end security of the entire data lifecycle.
Conclusion: A Call for Re-evaluation
Alex Hagenah’s discovery of the AIXHost.exe vulnerability in Microsoft Recall presents a clear and present danger to user privacy and data security. While Microsoft maintains that the issue does not constitute a vulnerability, the practical demonstration of data exfiltration without administrator privileges, after legitimate user authentication, paints a different picture for the cybersecurity community.
The "vault is solid, the delivery truck is not" analogy perfectly encapsulates the essence of the problem: a robust storage mechanism is undermined by a less secure processing pipeline. This flaw, combined with the inherently privacy-invasive nature of Recall, places users and organizations at significant risk.
For the sake of user trust, data integrity, and responsible AI deployment, Microsoft may need to re-evaluate its stance. A comprehensive fix that extends the robust security protections of the VBS enclave to all processes handling Recall data post-authentication is imperative. Until such measures are implemented, the prudent advice for users and enterprises alike will be to disable Recall or exercise extreme caution when considering its use, ensuring that the promise of AI-powered productivity does not come at the cost of fundamental privacy and security.